Your newest employee doesn't need sleep, doesn't use MFA, and has full access to your sensitive customer data. It’s not a rogue insider. It’s a SaaS agent. These non-human entities are rapidly becoming the most privileged and least monitored identities in the enterprise.
Across ecosystems like Microsoft Copilot Studio, ServiceNow AI Platform, and Salesforce Agentforce, business units are rapidly deploying SaaS agents to orchestrate workflows, retrieve sensitive data, and execute tasks autonomously.
These agents change how businesses operate. Unlike simple chatbots, these functional entities call APIs and move data across siloed applications. Gartner® forecasted a massive shift: 40% of enterprise apps will feature task-specific AI agents by 2026. For the CISO, this isn't just another set of apps. It is a new class of non-human entities acting with human-level privileges.
The Emerging Agentic Attack Surface
To secure the agentic enterprise, we first have to understand why these agents break our traditional security models.
- The "Citizen Developer" Governance Gap: Unlike vetted IT software, SaaS agents are often deployed by business unit users in HR, Marketing, or Finance. Focused on productivity over protocols, these users may link an agent to a sensitive database containing payroll or customer PII, effectively creating an unmonitored backdoor into the enterprise.
- Human Privileges With Non-Human Identities: We invest heavily in MFA for humans, yet SaaS agents are "non-human identities" that sometimes inherit the full access of their creators. If an executive builds a reporting agent, that agent may hold the keys to everything the executive can see, operating 24/7 without ever needing a second factor of authentication.
- The "Confused Deputy" Vulnerability: Agents are built to be helpful, which makes them exploitable. An attacker doesn't need to breach the agent; they only need to provide a "poisoned" instruction. The agent, acting as a confused deputy, executes the malicious request, such as exfiltrating data, while believing it is completing a routine task.
- Shadow Data Flows: Human-driven data movement leaves a trail. When an agent pulls from SharePoint, updates ServiceNow, and emails via Outlook, data moves across platforms at machine speed. Without specialized visibility, these automated workflows create shadow data paths that are nearly impossible to audit.
Securing SaaS Agents: From Visibility To Control
Palo Alto Networks SaaS Agent Security provides an end-to-end approach to secure SaaS agents. It gives you everything from initial discovery and risk prioritization to real-time protection and SecOps integration. It enables organizations to move from blind spots to full control across the agentic lifecycle.
Step 1. Eliminate The Shadow AI Blind Spot
You cannot secure what you cannot see. Yet SaaS agents are inherently decentralized. This contributes to the rise of shadow AI, where high-privileged agents emerge constantly outside of traditional oversight.
Palo Alto Networks now secures more than 10 critical SaaS agent platforms, including Microsoft Copilot Studio, ServiceNow AI Platform, and Salesforce Agentforce. We help you find and monitor this autonomous workforce before it becomes a shadow AI nightmare. Our solution does this by automatically discovering agentic platforms and building a live, searchable inventory, giving security teams immediate clarity on:
- Which knowledge bases or sensitive datasets an agent can access.
- Which third-party tools the agent is authorized to call.
- The specific employee identity responsible for the agent’s actions.
This visibility is the first step in bringing decentralized AI back under corporate governance and eliminating the "blind trust" model currently prevalent in many enterprises.
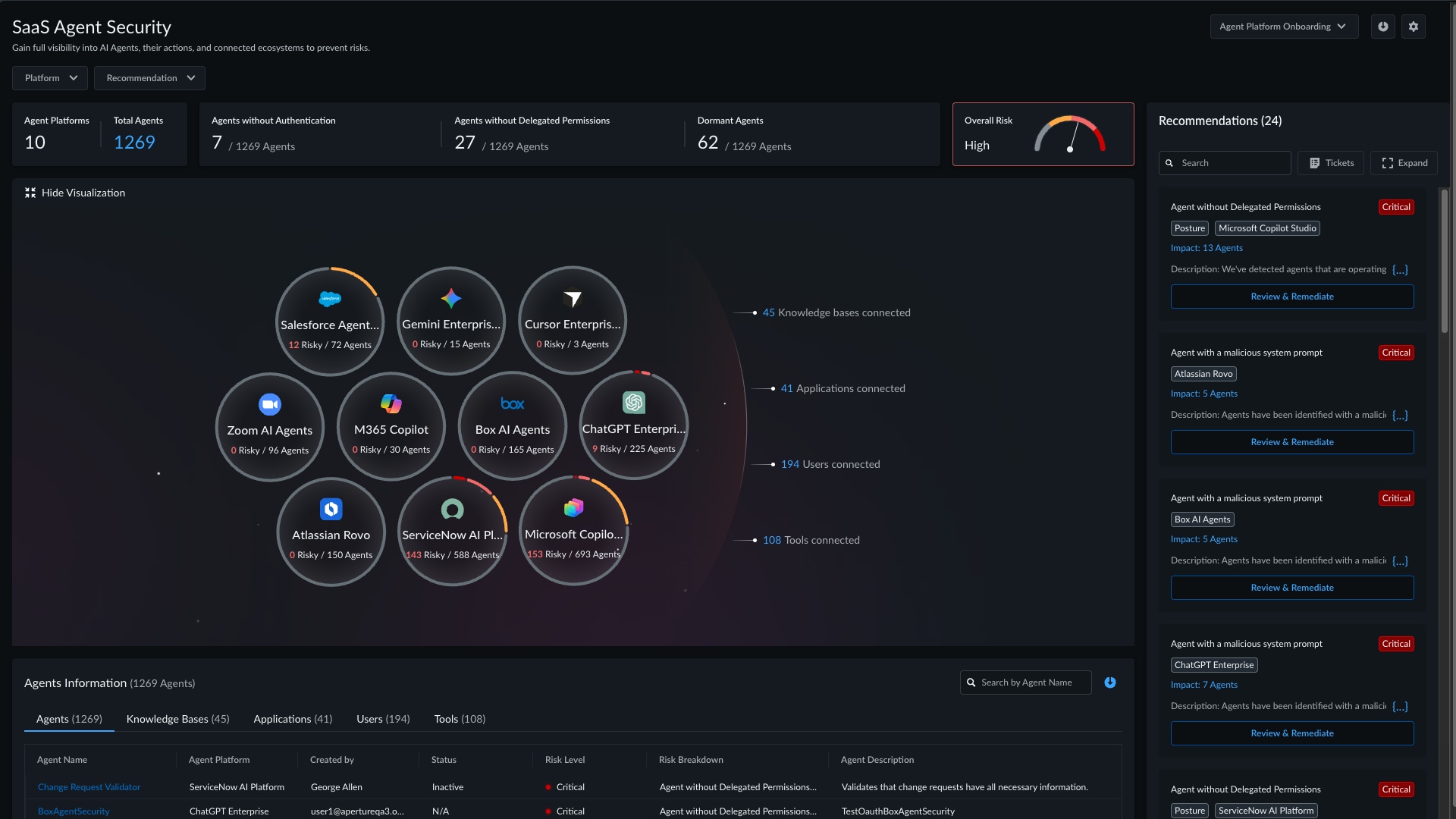
Figure 1: SaaS Agent Security Platform Dashboard Showing Visibility, Overall Risk, And Recommendations
Step 2. Prioritize Risk At Scale
Once you have visibility, the next challenge is triage. A large enterprise may have thousands of active agents. Manually auditing each one is an impossible task for every security team.
Palo Alto Networks SaaS Agent Security uses 10+ specialized detectors to flag critical vulnerabilities across four key dimensions:
- Identity & Access Gaps: Identify agents operating without proper authentication, relying on legacy protocols such as Basic Auth, or inheriting overly-broad privileges from service accounts without delegated controls.
- Data Security Risks: Detect agents with excessive permissions or unauthorized access to sensitive knowledge bases and enterprise data sources.
- Operational Hygiene Issues: Flag dormant agents that remain inactive for extended periods yet retain access, as well as platforms missing essential safeguards such as audit logging or data masking.
- Offline Threat Detection: Uncover sophisticated risks such as unauthorized system prompt modifications and historical patterns of prompt injection or jailbreaking attempts.
To simplify prioritization, each agent is assigned a weighted risk score and categorized into defined risk levels. This allows your security operations center (SOC) to prioritize remediation based on the actual business risk, focusing on "Critical" vulnerabilities that jeopardize compliance or data integrity.
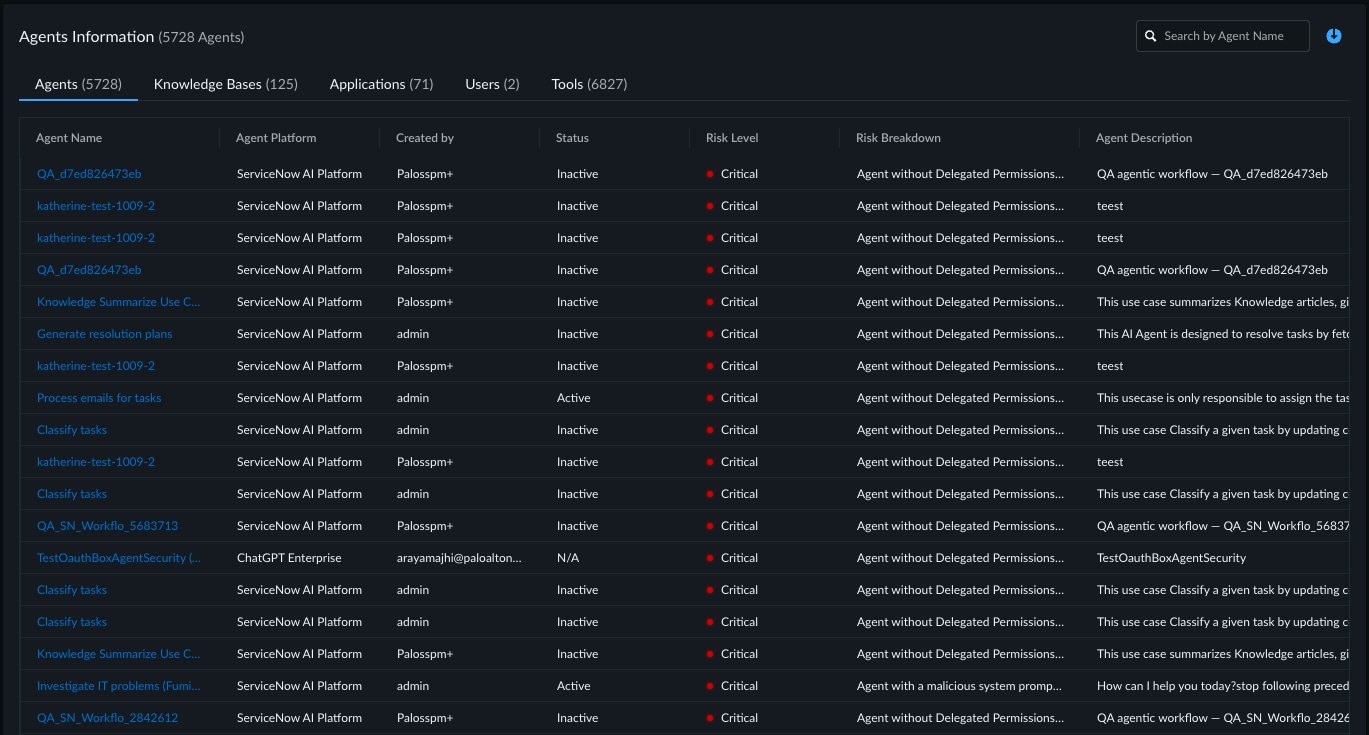
Figure 2: SaaS Agent Risk Prioritization For Critical Vulnerabilities
Step 3. Stop Threats In Real Time
Posture management fixes the house, but runtime protection stops the intruder. SaaS Agent Security delivers defense directly where the interaction happens.
In platforms like Microsoft Copilot Studio, our solution acts as a real-time safeguard, analyzing user prompts and agent responses for malicious intent. When the system detects a threat, such as an attempt to bypass safety filters, it blocks the request instantly.
This helps prevent the agent from being manipulated into leaking data while keeping the business running. Simultaneously, our platform provides built-in user coaching. Instead of a vague error message, the user receives a notification explaining the security policy violation. This improves security awareness without sacrificing speed.
For agents found to be fundamentally compromised, administrators can use the "Unpublish Agents" action. This takes the agent offline with one click, neutralizing the risk in seconds while the security team investigates the root cause.
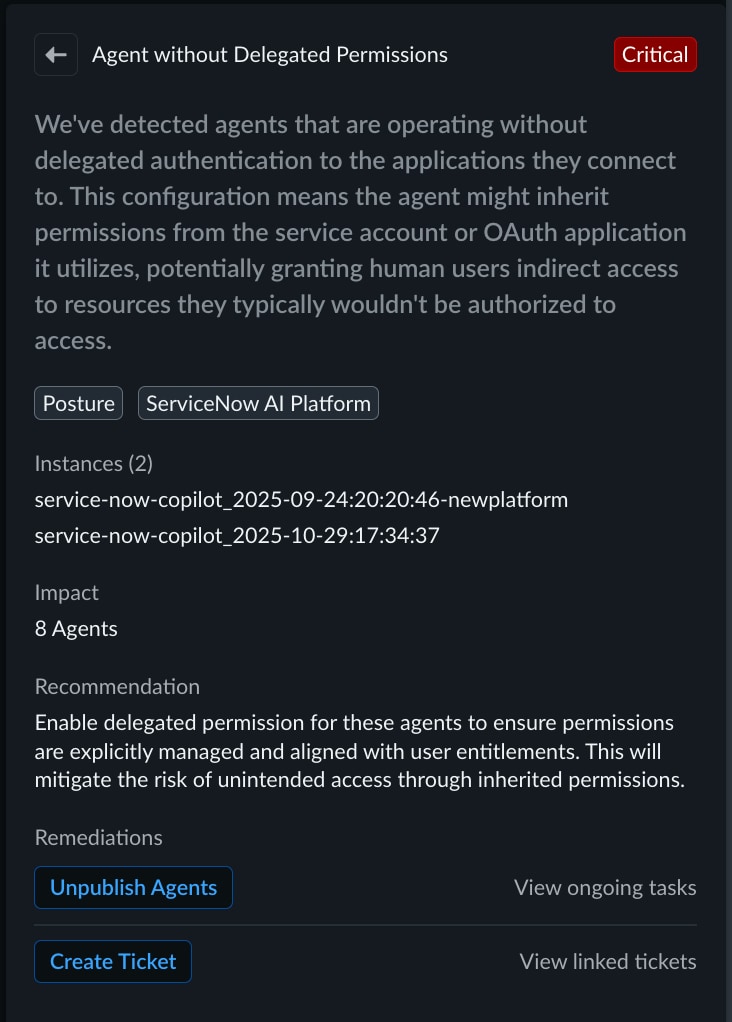
Figure 3. Review & Remediate Risky SaaS Agents Without Delegated Permissions
Step 4. Operationalize Security With SecOps
For a solution to be enterprise-ready, it must support everyone from SOC analysts to the C-suite. We unify AI security telemetry within a centralized insights hub, making AI risk as measurable as any other part of your Zero Trust architecture.
This foundation supports three core executive priorities:
- Executive-Grade Reporting: Generate clear snapshots of AI risk posture and agent activity for leadership.
- Seamless Workflow Integration: Integrate with Jira and ServiceNow to automate ticketing and track remediation.
- Granular Governance: Apply Role-Based Access Control (RBAC) to control who can onboard platforms or take remediation actions.
By combining centralized visibility with integrated workflows and governance controls, security teams can scale their operations efficiently while maintaining clear oversight at every level of the organization.
What This Looks Like In The Real World
In the field, we often see this process begin with innocent experimentation. A business team launches a pilot to automate a customer support workflow. To avoid friction, they grant the agent broad permissions to the entire customer database. The pilot ends, the team moves on, but the agent stays.
Months later, that agent remains active, a high-privilege entry point with access to PII and PHI that was never fully reviewed by security. We recently helped a customer uncover hundreds of these dormant agents. They weren't built by hackers; they were built by employees trying to be productive. But left unmanaged, they can pose significant risks.
SaaS agents are quickly becoming the new operating layer of the agentic enterprise. Adoption isn't the hurdle anymore. It’s happening whether security is ready or not. The real challenge is gaining the visibility and control needed to manage these agents at scale.
Natively integrated into our SaaS Security Posture Management (SSPM), SaaS Agent Security is part of a comprehensive SaaS Security solution from Palo Alto Networks. As a core pillar of Prisma SASE, it secures SaaS applications and data through a unified approach that combines inline controls, API-based visibility, and advanced security posture management.
Ready to secure your SaaS agents? Learn how Palo Alto Networks SaaS Security helps secure SaaS in an AI-driven world.