Identity has become one of the more complex parts of the enterprise to secure because it no longer lives in one place. It spans cloud roles, SaaS applications, identity providers, on-premises directories, privileged accounts and the access paths that connect them.
But identity risk rarely belongs to one account anymore. A single employee, contractor, developer or administrator can hold access across cloud platforms, SaaS applications, identity providers and on-premises systems. Each account may look manageable in isolation. Together, they can reveal excessive permissions, hidden administrative access, dormant accounts and privilege creep across the enterprise.
Fragmented access, however, creates exposure. Unit 42 analysis of more than 680,000 identities across cloud accounts found that 99% of cloud users, roles and services had excessive permissions, with some unused for 60 days or more. In practice, many identities carry privileges they don’t need day to day, giving attackers more room to escalate privileges, reuse credentials, abuse tokens and move laterally across environments.
Security teams often see pieces of the same person’s access across different systems. One console shows a cloud role. Another shows a SaaS login. Another shows an identity provider account. Without a unified human identity, teams are left piecing together access manually when they should be focused on reducing risk.
Why Account-Level Visibility Falls Short
Modern enterprises manage identity across disconnected control planes. On-premises directories, identity providers, SaaS applications and cloud platforms each maintain their own version of the user.
A single person may appear as an Active Directory profile, an Okta user, a cloud role, a SaaS login and a privileged admin account. Viewed separately, each account tells only part of the story. Viewed together, they show the full access footprint of a human identity.
AI is making that footprint harder to govern. As employees use AI assistants, SaaS copilots, automation tools and agentic workflows, human identities are increasingly connected to more applications, more data and more delegated actions across the enterprise. A single user account can now authorize AI driven activity, trigger workflows, access sensitive data or interact with systems at a speed and scale that traditional account-level reviews weren’t designed to capture.
The difference matters. Identity risk is often created by the combination of access across systems — inherited permissions, dormant accounts, administrative privileges, sensitive data access, AI connected applications and activity that appears normal in one environment but risky in context.
Without a unified view, teams are left manually stitching together identity data across consoles during the moments when speed is critical. As AI increases the number of tools, permissions and actions tied back to a single person, security teams need human-level identity context to understand where access creates real exposure.
What’s New with Cortex Cloud Identity Security: Unified Human Identities
Cortex CloudTM Identity Security now introduces Unified Human Identities, a capability that automatically correlates fragmented digital accounts into a single virtual identity asset.
Using user email as the primary identifier, Cortex Cloud correlates accounts across on-premises directories, identity providers, cloud platforms and SaaS applications. Each Unified Human Identity acts as an umbrella profile for every environment-specific account associated with one person.
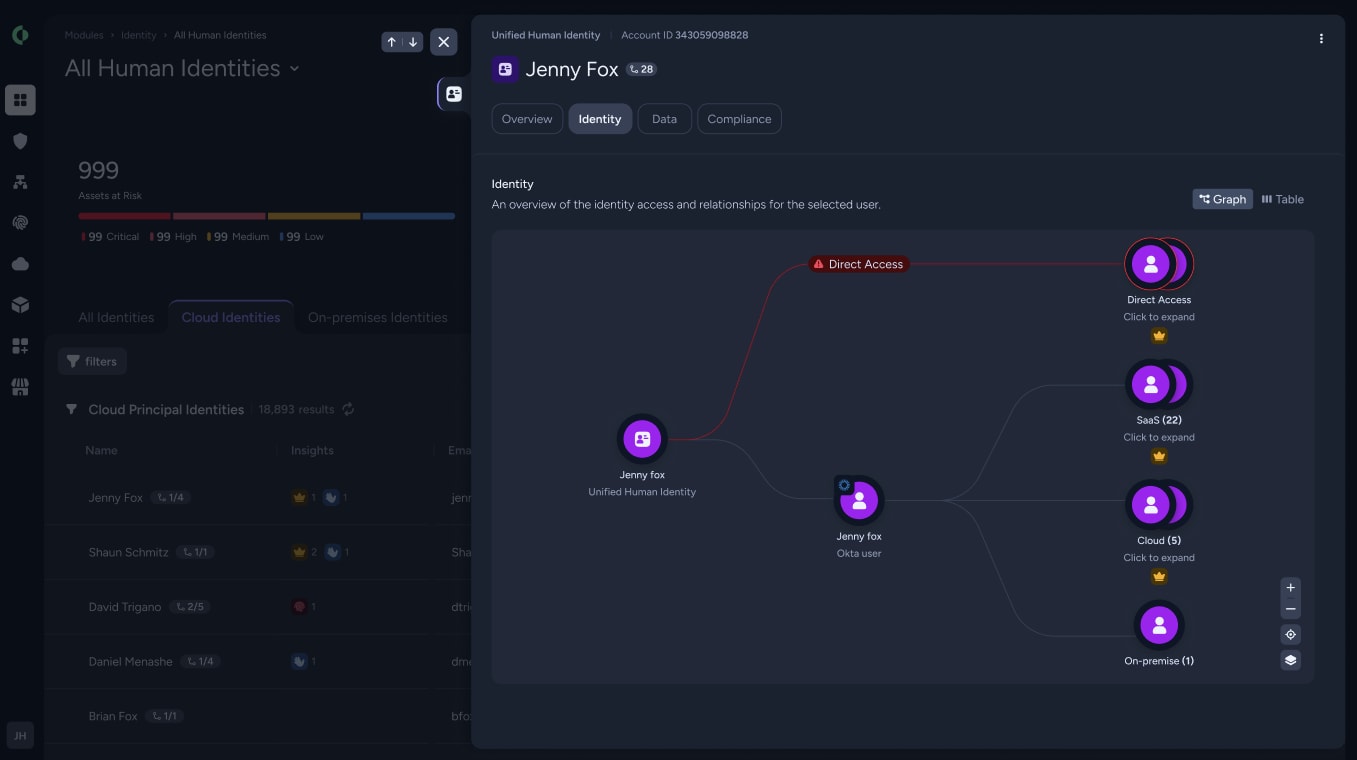
The result is one centralized view of the human behind the access, including:
- Identity metadata, such as title, department and employment type
- Providers contributing identity data, such as Okta, Active Directory, cloud platforms and SaaS applications
- Correlated accounts across cloud roles, directory profiles and SaaS logins
- Identity insights based on behavioral, posture and risk signals
- Administrative status across connected systems
- Activity context for inactive identities
- Risk breakdowns by severity
Instead of investigating access account by account, teams can understand how a person’s access adds up across the enterprise.
From Fragmented Accounts to Human Identity Context
Unified Human Identities changes identity investigation from an account-level exercise into a person-level view of risk.
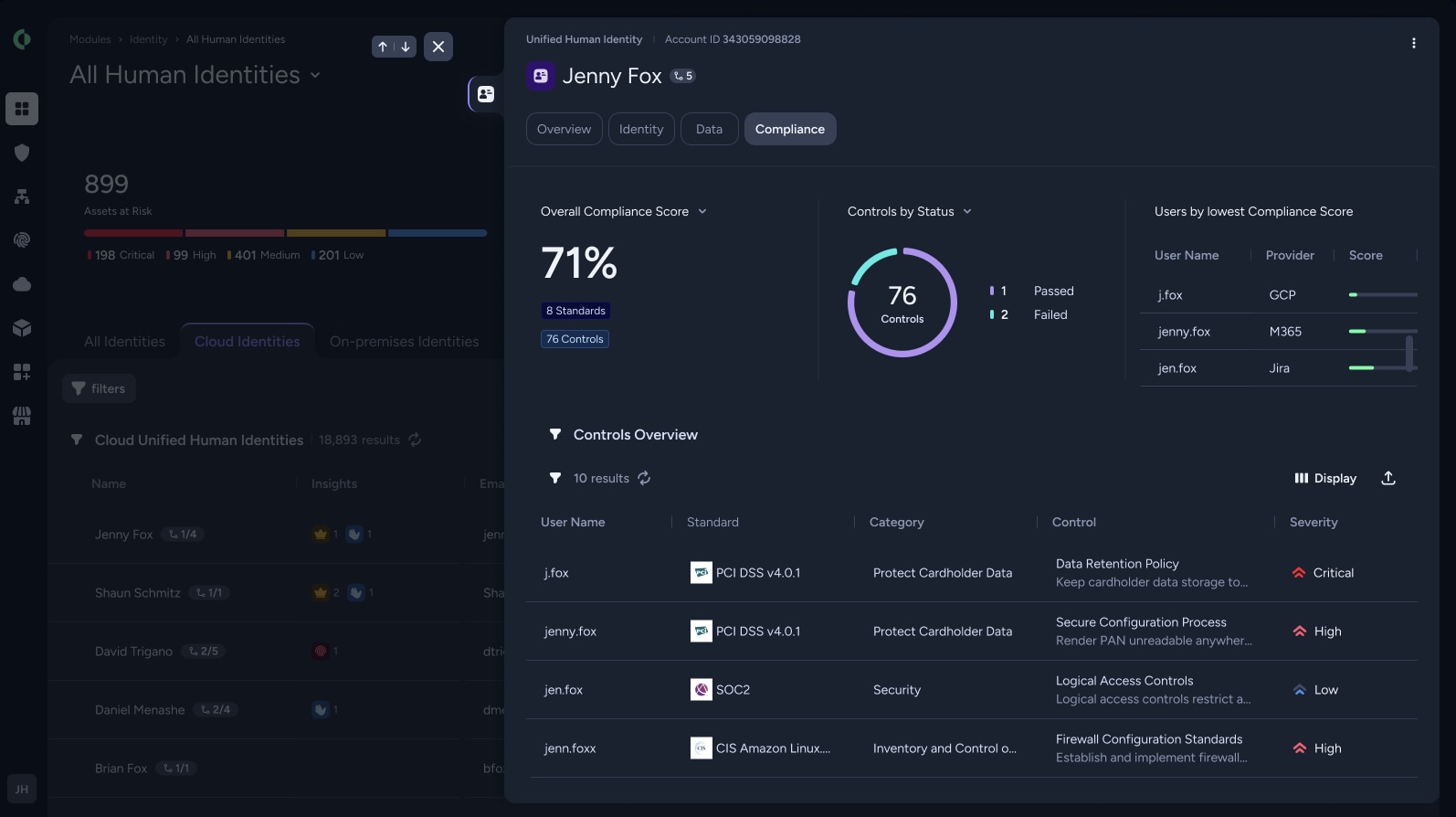
Security teams can use the Human Identities inventory to audit individuals across the organization and filter by all identities, cloud identities, SaaS identities and on-premises identities. From there, they can open an identity details panel to see the providers, correlated accounts, insights and risks tied to a specific person.
A cloud account may look low risk in isolation. But when it’s connected to the same person’s SaaS login, identity provider account and privileged admin access, it may reveal excessive permissions, dormant access or exposure to sensitive resources.
With person-level context, teams can identify privilege creep, investigate identity-related incidents, and prioritize risk based on the full access footprint behind a human identity.
Turning Human Identity Context Into Action
Human identity context helps teams move faster across cloud, SaaS, identity provider and on-premises environments.
Cloud security teams can see total effective access, excessive permissions and administrative exposure. ITDR teams can investigate suspicious behavior with the context needed to understand whether activity is isolated or part of a broader identity risk pattern. SaaS and data security teams can connect user access to sensitive applications, data and business impact.
Context is becoming even more important as AI expands what human identities can do. A single person’s access may now connect to AI assistants, SaaS copilots, automation workflows and delegated actions across the enterprise. Without a unified view, teams may see the account behind an action but miss the full identity exposure behind the person.
By correlating fragmented accounts into one human identity profile, Cortex Identity Security helps teams understand whose access creates risk and where to act first.

Take Control of Human Identity Risk
Attackers increasingly rely on valid access, while fragmented identity systems slow down investigations and make least privilege harder to enforce across environments that continuously change.
Unified Human Identities helps close the gap between intended controls and real-world access. By correlating fragmented accounts into one human identity profile, Cortex Identity Security gives teams the context to understand who has access, where risk exists, and how identity exposure spans cloud, SaaS, identity provider and on-premises environments.
Learn More
Security teams can no longer afford to investigate identity risk one account at a time.
Ready to take control of your identities? Book a demo to see how Cortex Identity Security helps teams reduce identity-driven risk, contain exposure, and enforce least privilege across cloud, SaaS, identity provider and on-premises environments.