ASM BUYER’S TOOLKIT
All form fields required
What You’ll Learn
WHY ASM is essential in a complex digital world
HOW a strong ASM platform makes all the difference
WHO has strong capabilities according to independent GigaOm
WHAT resources you need for executive buy-in
ASM Solution Includes:
- Independent Market Analysis
- Use Case Studies
- CISO Guide
- Active Response Datasheet
- RFP Checklist
Why Now Is the Time for ASM
Get independent ESG insights on the value that ASM brings to the challenging modern world where attack surfaces are dynamic, growing and vulnerable. Understand how an ASM platform can significantly reduce risk, streamline SecOps and ultimately lower costs.
Key Value Drivers
- How attack surface weaknesses lead to security incidents.
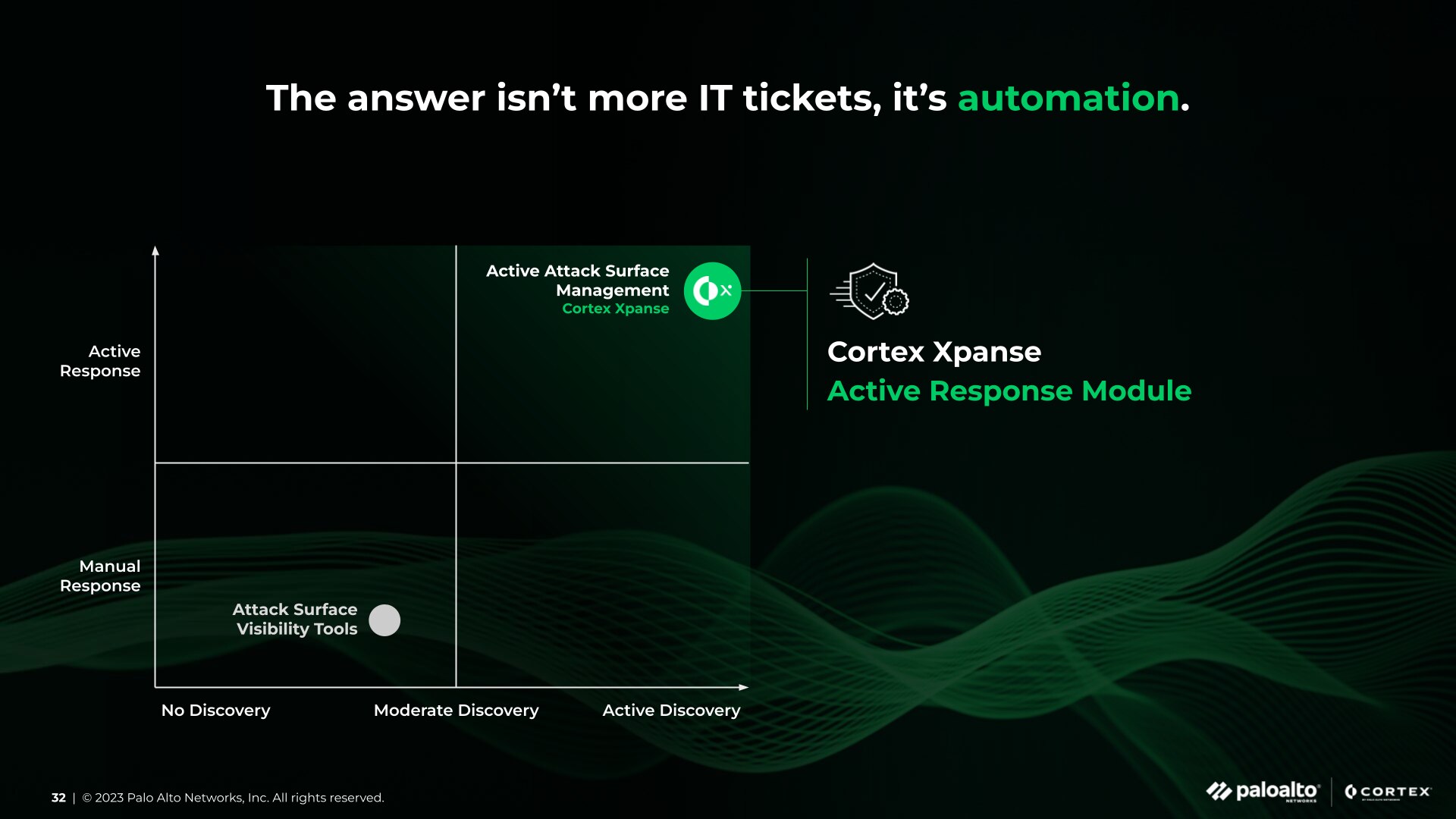
- Why it’s time for ASM automation.
- How ASM can fit into your security budget.
Top 10 Attack Surface Management Use Cases
How Xpanse ASM enhances cybersecurity is in the details. Use cases not only help cybersecurity teams understand how Xpanse works, they help teams make the case to internal stakeholders. Use this case study deck and webinar to take next steps for enabling Xpanse ASM benefits.
KUPPINGERCOLE LEADERSHIP COMPASS FOR ATTACK SURFACE MANAGEMENT (ASM) RESULTS
Assess and Select the Best ASM Solution
Dive into the 2023 report, “KuppingerCole Leadership Compass for Attack Surface Management.” The in-depth analysis reveals why independent experts at KuppingerCole rated Cortex Xpanse® an Overall, Product, Innovation and Market Leader with our Active Attack Surface Management platform.

Things to Consider When Buying an ASM Solution
Learn about core capabilities and features to look for when selecting an ASM vendor. These insights will help security teams and leaders evaluate their options and confirm which ASM platform is ideal for them.
A Peek into What’s Inside
- What ASM technical requirements to look for.
- An informative checklist when buying an ASM solution.
- How ASM can be leveraged by multiple teams.
- Risks and successes that CISOs should look for.