- Machine Identity Security: The Definitive Guide
- What Is a Certificate Chain of Trust?
- What Is a Certificate Authority?
- TLS Certificate Risks: Vulnerabilities and Mitigation Strategies
- What Is a TLS/SSL Port? Port 443 and HTTPS Explained
-
What Is Certificate Pinning? Benefits, Risks & Best Practices
- Certificate Pinning Explained
- How Certificate Pinning Works
- Listiche: Key Stages of a Pinning Failure
- Types of Certificate Pinning
- Listiche: Static vs. Dynamic Pinning
- Why Pinning Is Essential for Zero Trust
- Certificate Pinning vs. Standard SSL/TLS
- Benefits of Certificate Pinning
- Risks and Limitations of Certificate Pinning
- When to Use Certificate Pinning
- When to Avoid Certificate Pinning
- Certificate Pinning Best Practices
- Certificate Pinning and Machine Identity Security
- FAQs
- What Is ACME Protocol?
- What Is Workload Identity? Securing Non-Human Identities
- What Is a Non-Human Identity (NHI)? Machine Identity Security Explained
- What is Code Signing? Benefits, Risks & Implementation
-
TLS/SSL Offloading: Definition & Decision Checklist
- TLS/SSL Offloading Explained
- SSL Termination vs. SSL Bridging
- Key Differences in Workflow
- Unit 42 Perspective: Risks of Uninspected Traffic
- Benefits for Security and Infrastructure Teams
- CISO Decision Checklist: SSL Termination vs. SSL Bridging for Compliance
- Detailed CISO Decision Checklist
- Summary Recommendation for CISOs
- TLS/SSL Offloading FAQs
- What Is a Multi-Domain SSL Certificate? SAN & UC Explained
-
What Is a Machine Identity?
- How Do Machine Identities Work?
- Machine Identity Management (MIM) vs. Human IAM
- Architecture Components and Identity Types
- Secrets Management vs. Machine Identity Management
- Lateral Movement and Attacker Workflow
- Cloud Security Implications and CIEM
- Implementation Steps for Machine Identity Security
- Machine Identity FAQs
-
What Is Cert-Manager? Kubernetes Certificate Management Explained
- cert-manager Explained
- Core Components: Issuers and Certificates
- 1. Issuers and ClusterIssuers
- 2. Certificates
- How cert-manager Automates Machine Identity
- Common Compatible Cloud Platforms
- Zero Trust and Kubernetes Security Alignment
- Integrating cert-manager into DevSecOps Workflows
- Benefits for DevSecOps Teams
- cert-manager FAQs
- What Is an X.509 Certificate? Definition, Standards, and Role
-
What Is TLS Certificate Renewal? Process, Risks & Automation
- TLS Certificate Renewal: The Shift from Maintenance to Mission-Critical
- Why the 47-Day Mandate Redefines Renewal Strategy
- The Technical Lifecycle of a TLS Renewal
- Critical Risks: The High Cost of Renewal Failure
- Best Practices for Enterprise-Scale Renewal
- Overcoming Common Renewal Challenges
- TLS Certificate Renewal FAQs
-
What Is Certificate Validation? Guide to Best Practices
- Certificate Validation Explained
- The Role of Certificate Authorities and the Chain of Trust
- The Hierarchy of Trust
- The Sequence of the Validation Process
- Types of Certificate Validation Levels
- Unit 42 Insights: The Risk of Identity Exposure
- Threat Behavior Observations
- Troubleshooting Common Validation Failures
- Certificate Validation FAQs
-
What is SPIFFE? Universal Workload Identity Framework Guide
- SPIFFE Explained: Solving the Workload Identity Problem
- Core Components of the SPIFFE Standard
- The SPIFFE Workload API
- Why Traditional Secret Management Fails in Cloud-Native Environments
- The Problem of "Secret Zero"
- Vulnerabilities of Static Credentials and Long-Lived Tokens
- IP-Based Security vs. Identity-Based Security
- How SPIFFE Implementation Works: The Attestation Process
- The Role of SPIRE as the Reference Implementation
- Critical Use Cases for Enterprise Security
- SPIFFE FAQs
- What Is Certificate Management?
- What Is a Self-Signed Certificate? Risks, Uses & Best Practices
- What Is a TLS Certificate? How TLS Secures Web Communication
- What is Cloud Workload Security? Protection & Best Practices
-
What Is the TLS Certificate Lifecycle? Implementation Guide
- TLS Certificate Lifecycle Explained
- The 6 Core Stages of the TLS Certificate Lifecycle
- Why TLS Certificate Lifecycle Matters
- Key Causes of Certificate Failure
- Validation Checks: CRL and OCSP
- How Automation Improves TLS Certificate Lifecycle
- TLS Certificate Lifecycle and Zero Trust
- TLS Certificate Lifecycle FAQs
- What Is PKI? Public Key Infrastructure & Authentication Guide
- Security Standards and Compliance: SSL/TLS Best Practices
-
What Is the TLS Handshake? Process, Steps, and Best Practices
- The Strategic Importance of the TLS Handshake
- How the TLS Handshake Works: Step-by-Step
- TLS 1.2 vs. TLS 1.3: Evolution of Speed and Security
- The Role of Cipher Suites and Digital Certificates
- Identifying and Resolving TLS Handshake Failures
- Advanced Security: TLS Fingerprinting and Threat Detection
- TLS Handshake Best Practices
- TLS Handshake FAQs
- What Is an SSL Stripping Attack?
What Is TLS Decryption?
TLS Decryption is the security process of intercepting and unscrambling encrypted data as it travels across a network to inspect it for malicious content. By temporarily "breaking" the encryption envelope, security tools can analyze the plaintext payload for threats like malware, data exfiltration, or command-and-control (C2) communications that would otherwise stay hidden within an encrypted tunnel.
Key Points
-
Threat Visibility: Unmasks hidden malware and exploits lurking in encrypted HTTPS traffic. -
Data Protection: Prevents sensitive information from being leaked through encrypted channels. -
Policy Enforcement: Enables granular control over web applications and user activities. -
Performance Balancing: Requires dedicated hardware or optimized software to minimize network latency. -
Privacy Compliance: Needs careful configuration to bypass sensitive traffic like healthcare or banking data.
TLS Decryption Explained
In a modern enterprise, over 90% of web traffic is encrypted using transport layer security (TLS). While encryption is vital for privacy, it creates a massive blind spot for security teams. Threat actors frequently use this same encryption to bypass legacy firewalls, delivering payloads or stealing data without detection.
TLS decryption acts as a "security checkpoint." It allows a security device, such as a next-generation firewall (NGFW), to act as a middleman. The device decrypts the traffic, scans it using threat prevention engines, and, if safe, re-encrypts it before sending it to the final destination. This ensures that the benefits of encryption remain intact for the journey across the public internet while maintaining network security at the perimeter.
How TLS Decryption Works
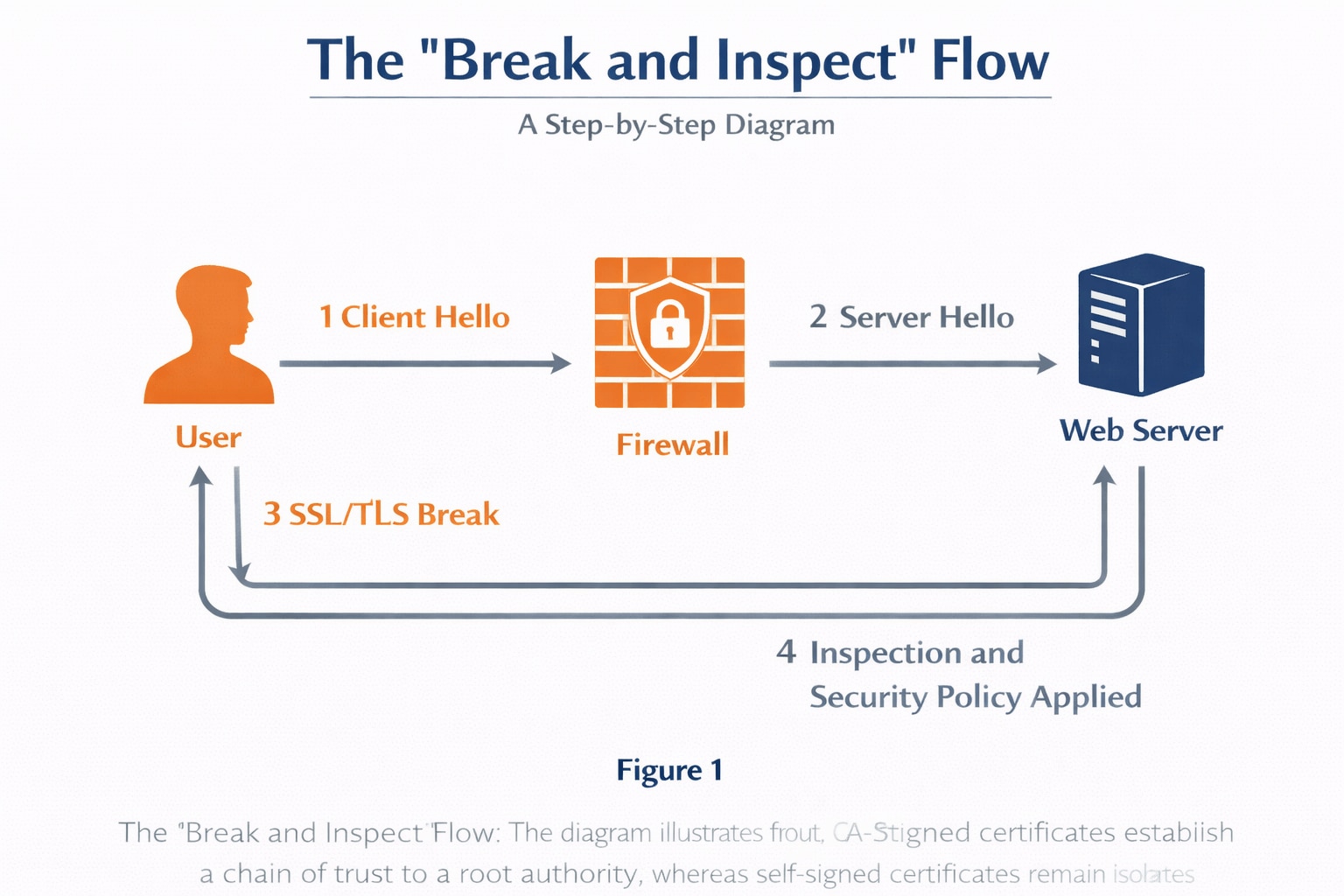
The process generally follows a "Break and Inspect" model. When a user attempts to connect to a secure website, the decryption-capable device intercepts the request.
The Decryption Workflow
- Interception: The firewall intercepts the client's request to a server.
- Proxy Handshake: The firewall establishes a secure connection with the destination server on behalf of the client.
- Certificate Generation: The firewall generates a new certificate for the destination hostname, signed by the organization's internal Certificate Authority (CA), and presents it to the client. The client trusts this certificate because the internal CA is in its trust store.
- Inspection: The firewall decrypts the incoming traffic from the server, scans for threats, and applies security policies.
- Re-encryption: Clean traffic is re-encrypted and sent to the client.
| Feature | Inbound Decryption | Outbound Decryption (Forward Proxy) |
|---|---|---|
| Primary Use | Protecting internal servers/web apps | Protecting internal users visiting the web |
| Control | The organization owns the server certificates | The organization uses a trusted internal CA |
| Threat Focus | Exploits against web servers | Malware downloads and data exfiltration |
Methods of Decryption: Passive vs. Active
Organizations must choose between passive and active methods based on their specific visibility and performance requirements.
1. Passive Decryption (Mirroring)
Passive decryption involves out-of-band inspection. The security tool receives a copy of the traffic, which is sent along with the server’s private key (for non-PFS ciphers), allowing it to decrypt and inspect without adding latency to the live flow.
2. Active Decryption (Forward Proxy)
Active decryption is the standard for modern identity security and threat prevention. The security device sits inline, meaning it can actively block threats in real-time.
3. Endpoint-Based Inspection
Instead of a network device, software agents on the user’s device perform the inspection. While this offers granular visibility, it can be resource-intensive and difficult to manage across a diverse device fleet.
The Role of TLS Decryption in Zero Trust
TLS decryption can complement zero trust architectures by adding content inspection to identity-based controls. You gain visibility into what’s happening inside encrypted sessions, which identity alone cannot provide.
- Enforcing Least Privilege: Decryption enables the firewall to view the specific URLs and applications, supporting more precise web filtering and access policies.
- Preventing Lateral Movement: Attackers often utilize encrypted channels to move between systems. Decryption helps identify these threat behaviors inside the network.
- Continuous Monitoring: Decryption can extend inspection to encrypted traffic that would otherwise be invisible to network controls, subject to policy-based bypass for sensitive or regulated traffic.
Technical Challenges: TLS 1.3 and Performance
The transition to TLS 1.3 has introduced complexities. Unlike previous versions, TLS 1.3 encrypts the handshake process itself and mandates the use of PFS.
Performance Impact Factors
- CPU Overhead: Decrypting and re-encrypting traffic is mathematically intensive.
- Latency: Every "break and inspect" step adds milliseconds to the round-trip time.
- Scale: As encrypted traffic volume grows, hardware must be sized correctly to avoid becoming a bottleneck.
Solutions to Performance Issues
- Hardware Acceleration: Using dedicated chips (ASICs) to handle cryptographic operations.
- Selective Decryption: Only decrypting high-risk traffic categories while bypassing trusted sites.
- Dedicated Decryption Brokers: Offloading decryption tasks to a specialized device that feeds plaintext to multiple security tools.
Operational Best Practices and Privacy
Implementing TLS decryption requires a balance between security and the legal right to privacy.
Strategic Implementation Steps
- Define Bypass Lists: Never decrypt traffic for sensitive categories like Finance, Healthcare, or Government. This maintains compliance with regulations like HIPAA and GDPR.
- Internal CA Distribution: Ensure the internal CA certificate is pushed to all managed devices to avoid "Untrusted Connection" warnings for users.
- Start Small: Begin with a subset of users or specific high-risk URL categories (e.g., "Newly Registered Domains") before a full-scale rollout.
- Audit and Monitor: Regularly review decryption logs to ensure the system isn't breaking critical business applications.